Pros, Cons, and Security Considerations About BYOD
Pros, Cons, and Security Considerations About BYOD January 14, 2025 In today’s workplace, employees expect flexibility in their work environments, and one of the most prominent trends that has emerged is Bring Your Own Device (BYOD). This policy allows employees to use their personal devices—smartphones, tablets, laptops, or even wearables—for work purposes. While this can […]
Unlocking the Future and Understanding Quantum Computing
Unlocking the Future and Understanding Quantum Computing January 10, 2025 Quantum computing is often portrayed as the next frontier in technology, promising to revolutionize fields ranging from cryptography to drug discovery. While the concepts can seem daunting, grasping the basics of quantum computing, exploring its potential applications, and preparing for its implications in the IT […]
Embracing Human-Centric Technology: Putting People First in Innovation

Embracing Human-Centric Technology: Putting People First in Innovation January 7, 2025 In an increasingly digital world, the importance of human-centric technology cannot be overstated. As we develop tools and systems, prioritizing user needs, fostering empathy, and finding the right balance between automation and human interaction are crucial. In this blog, we’ll explore how to design […]
The Transformative Power of 5G Technology

The Transformative Power of 5G Technology January 3, 2024 The advent of 5G technology marks a significant leap forward in mobile communication, promising faster speeds, lower latency, and enhanced connectivity. Beyond just faster internet on smartphones, 5G is set to transform industries and enable a myriad of new applications. Let’s explore how 5G is reshaping […]
Sustainable IT Practices: Paving the Way for a Greener Future

Sustainable IT Practices: Paving the Way for a Greener Future December 31, 2024 As businesses increasingly recognize the importance of sustainability, the IT sector has a crucial role to play in reducing carbon footprints and promoting eco-friendly practices. Sustainable IT practices not only benefit the environment but can also lead to cost savings and improved […]
Exploring Cloud Computing Innovations: Multi-Cloud Strategies, Edge Computing, and Cloud-Native Development

Exploring Cloud Computing Innovations: Multi-Cloud Strategies, Edge Computing, and Cloud-Native Development December 27, 2024 Cloud computing continues to evolve, reshaping how businesses operate and leverage technology. As organizations increasingly recognize the benefits of cloud solutions, they are also navigating the complexities of multi-cloud strategies, the rise of edge computing, and cloud-native development. In this blog, […]
Here’s What You Should Know About the Cloud

Here’s What You Should Know About the Cloud December 24, 2024 Today, where digital transformation is at the forefront of business strategy, the term “cloud” has become ubiquitous. But what does it really mean, and how can it benefit you or your organization? Let’s dive into what you might already know about the cloud and […]
Machine Learning, AI, and Deep Learning
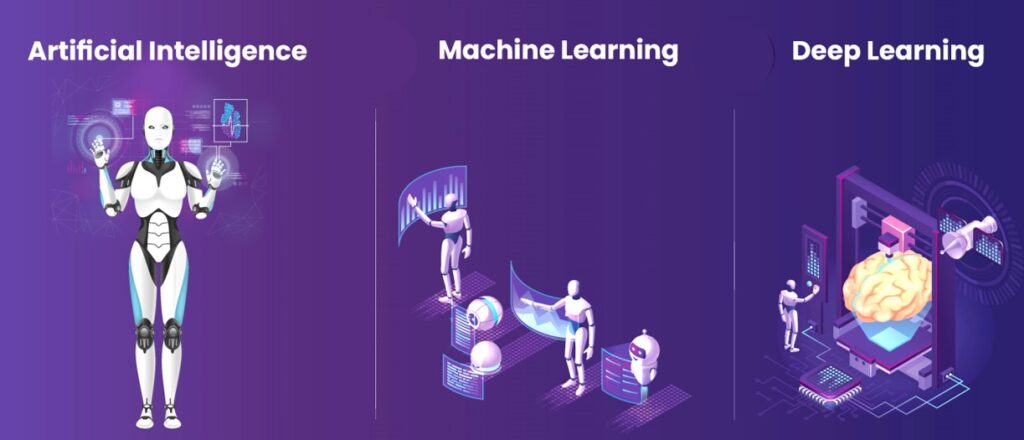
Machine Learning, AI, and Deep Learning December 20, 2024 In the realm of technology, terms like artificial intelligence (AI), machine learning (ML), and deep learning (DL) are often used interchangeably. However, they refer to distinct concepts that represent different levels of sophistication in computational intelligence. This blog post aims to clarify these terms and illustrate […]
Shining the Spotlight on Deep Learning
Shining the Spotlight on Deep Learning December 17, 2024 In recent years, deep learning has emerged as a transformative technology, driving advancements across various industries. From self-driving cars to voice recognition and medical diagnosis, deep learning is reshaping the way we interact with technology. But what exactly is deep learning, and how can it benefit […]
The Development of Machine Learning and AI in IT

The Development of Machine Learning and AI in IT December 13, 2024 In recent years, artificial intelligence (AI) and machine learning (ML) have transitioned from buzzwords to vital components of the information technology (IT) landscape. As organizations strive for greater efficiency, improved decision-making, and enhanced security, AI and ML are proving to be game changers. […]
